Researcher detects hackers’ on facebook server

So share our every personal detail on Facebook without thinking twice about the safety of that information. We don’t care much about the incidents like this. But imagine what if someone else can also upload anything in your profile!
Facebook bug bounty programme
According to Orange Tsai, a security researcher participating in a Facebook bug bounty programme, once he entered into the security of a server belonging to the social network he discovered evidence that at least one other hacker had already been there, and had gathered hundreds of passwords from Facebook employees. He works at Taiwanese computer security company. Tsai said, he tested a server located at files.fb.com, which hosted a file transfer application made by Accellion, which is used by Facebook employees for file sharing.
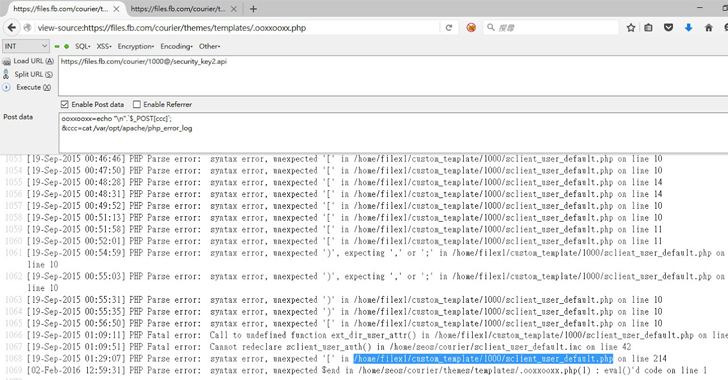
After finding a number of loopholes in the Accellion software, he made it to the server – but when he analyzed the server logs, he discovered errors suggesting that someone else had already been there.
What is important is that the earlier hacker had installed a PHP-based backdoor that allowed them to execute shell commands, and had taken control of the Accellion software’s authentication process, Which means the access to the credentials of the users.
Tsai said in an advisory, “At the time I discovered these, there were around 300 logged credentials dated between February 1st to 7th, mostly ‘@fb.com’ and ‘@facebook.com’. Upon seeing it I thought it’s a pretty serious security incident.”
What it takes to hack facebook server
He added that the software provided access to users to log in with LDAP and Windows Active Directory credentials, meaning the hacked login credentials could possibly have been used for other Facebook corporate servers.
The evidence showed downloading of captured credentials. Tsai said that hackers deleted the captured credentials file every few days. Hackers also appeared to have tried to map Facebook’s internal network, log into LDAP and other servers and search for SSL private keys.
He said that hacking has been done twice. Once in July and the second time in mid-September. The first breach of July occurred around the time of the public disclosure of a remote code execution bug in the Accellion File Transfer Appliance.

But the second breach, which was possibly have done by another hacker was more serious. Because this time the hackers installed key logging software. And Tsai tested the server in February.
Tsai reported his research to Facebook, which brought him a reward of $10,000 (£7,000) bug bounty. Later Facebook started its own investigation, which ended this month.
Facebook server is safe: Facebook
Facebook said that its servers were secured and one member from the Facebook security team said that Tsai founded the evidence left behind by another penetration tester who participated in the bounty programme but avoided to present information to Facebook.
Facebook security engineer Reginaldo Silva said in a statement on Hacker News (a tech-oriented news board operated), After the incident response, we determined that the activity Orange detected was in fact from another researcher who participates in our bounty programme.” He added that the hacked system was not connected from those that host data shared by users on Facebook.
Silva avoided giving a response to a Hacker News user who indicated that installing a keylogger, downloading login details and not informing Facebook displayed not white-hat penetration testing but rather “an actual compromise of employee credentials”.
There was no immediate response from the Facebook.
